Welcome to Privacy Policy Online.
Welcome to Privacy Policy Online. Here you can generate your own Privacy Policy to comply with international laws on user data privacy (CCPA, CalOPPA, GDPR) and the requirements of leading Advertising and Affiliate Networks, such as Google AdSense or Commission Junction.
On our site you will find not only a generator for quickly and easily generating a Privacy Policy for your sites, but also find many other resources for complying with regulations and learning more about Privacy Policies.
New Terms & Conditions + Disclaimer Generators are now available.
↓
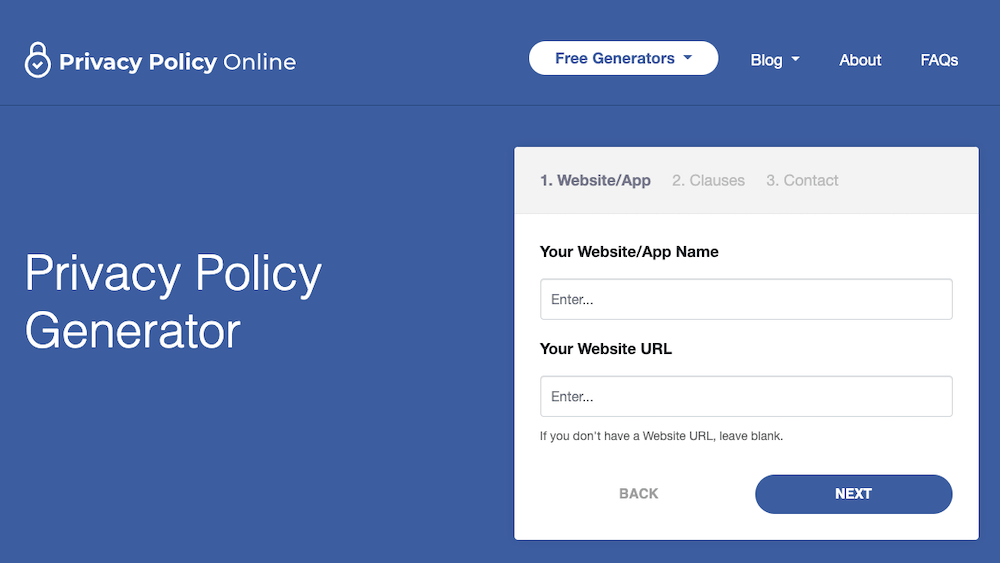
Privacy Policy Generator
Use this simple web form to generate a Privacy Policy document for your website.
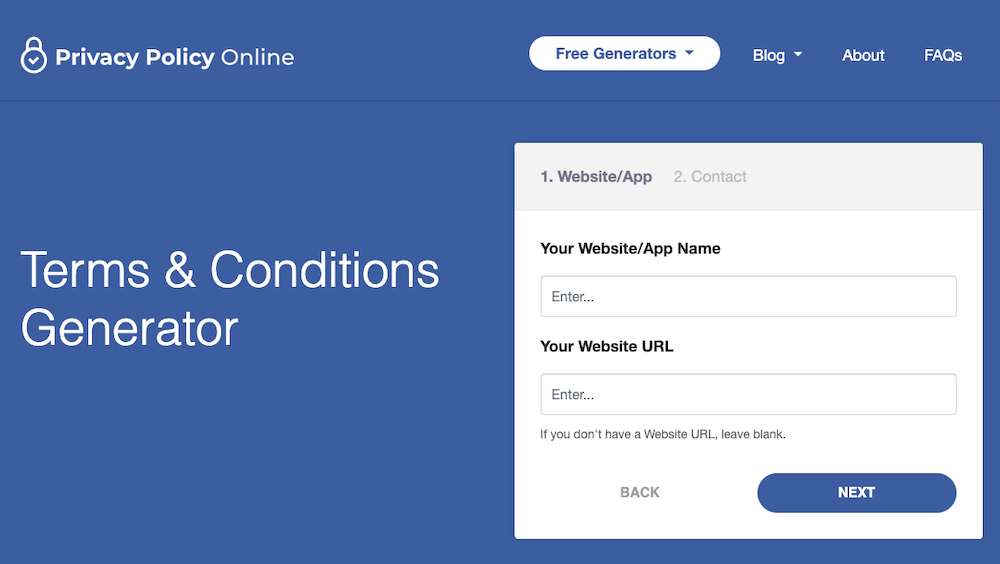
Terms & Conditions Generator
Use this simple web form to generate a Terms & Conditions document for your website.
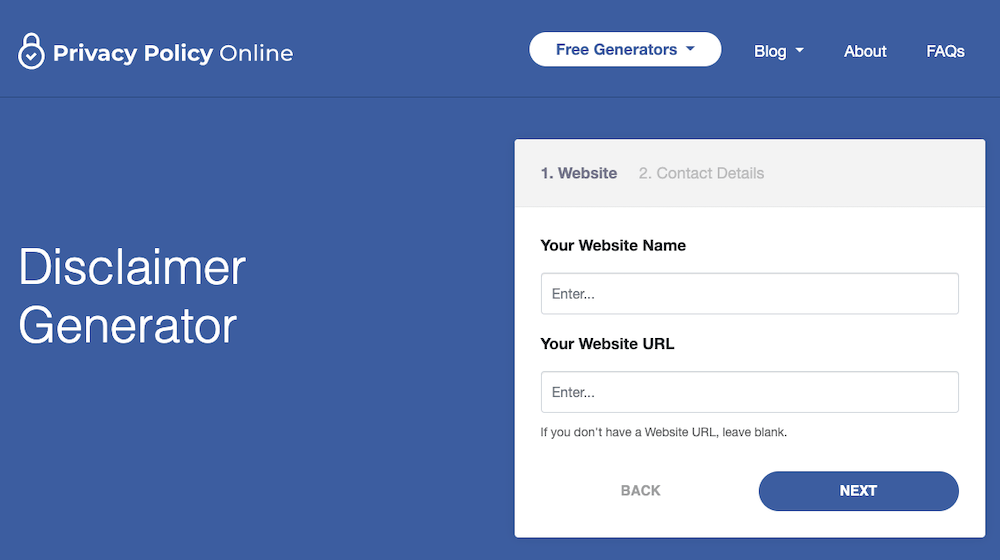
Disclaimer Generator
Use this simple web form to generate a Disclaimer document for your website.
Blog

What Is A Privacy Policy?
A Privacy Policy is a legal document that discloses some or all of the ways a website gathers, uses, shares, discloses and/or manages a website visitor's data.

Sample Privacy Policy Template
We have gotten many requests for a standard Privacy Policy Template, so here it is! Simply replace the bracketed fields with your own information. Voilà!
What Are Cookies?
Also known as browser cookies or tracking cookies, cookies are small, usually encrypted text files, located in your browser's directory.